 4 minutes
4 minutes
What’s New in the Payara Platform March 2026 Release?
The March 2026 release brings important platform modernization, stability improvements, and comprehensive bug fixes across the Azul Payara Platform […]


The Remote Code Execution (RCE) vulnerability detected in the Spring Java Framework in March 2022 (tagged as CVE-2022-22965) is unlikely to impact those using Payara Platform.
However, users that deploy Spring Framework WAR packaged applications in Payara Server are affected by this vulnerability as Payara Server shares pieces of code in its Servlet implementation, Catalina, which was originally branched from Apache Tomcat.
To mitigate the risk of being impacted by this vulnerability, we have implemented an urgent fix that effectively disables the affected code in the corresponding Catalina modules. This hotfix will be included in the upcoming releases of both Payara Community (5.2022.2) and Payara Enterprise (5.38)
Please note: Users must also apply the fixes issued in Spring Framework 5.3.18 and 5.2.20, available in Spring Boot 2.6.6. as per their recommendations, to be fully protected.
Read more about the vulnerability here:
Find more resources here for increasing the security of your applications:
Share:
 4 minutes
4 minutes
The March 2026 release brings important platform modernization, stability improvements, and comprehensive bug fixes across the Azul Payara Platform […]
 7 minutes
7 minutes
If you worked with MicroProfile Health, you already understand the value of exposing application health information through standardized endpoints. […]
 1 minute
1 minute
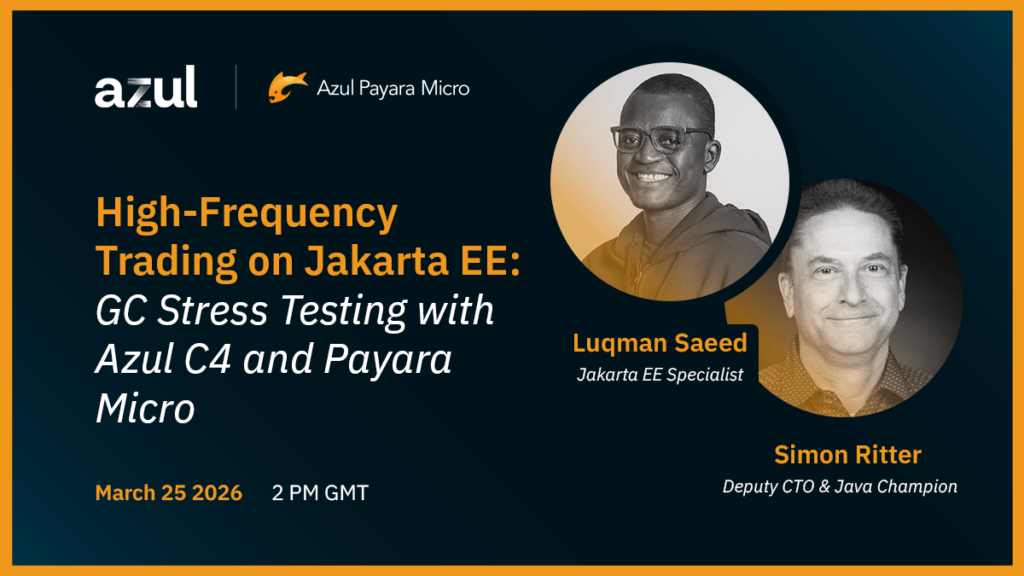
Modern high-frequency trading (HFT) platforms operate under extreme performance constraints, processing tens of thousands of messages per second while […]